Wiper: la nueva modalidad de Malware que 'limpia' o causa una pérdida permanente de datos - C2USER CISOS LAB
Three Ways to Protect Your Business Against Wiper Malware: The Growing Cyber Threat - United States Cybersecurity Magazine

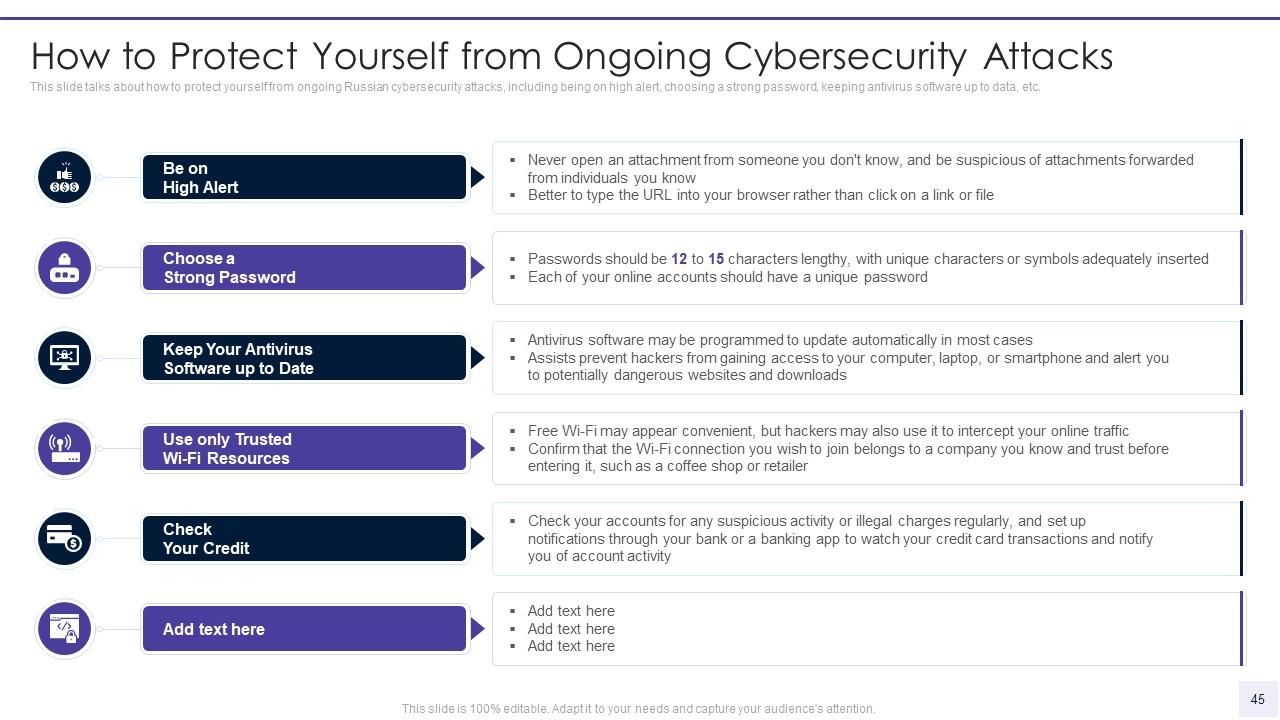
War In Ukraine: What Is Wiper Malware That Russia May Be Using For Cyber Attacks On Ukraine - News18